目录
网络工程师成长日记340-某邮政防火墙
这是我的第340篇原创文章,记录网络工程师行业的点点滴滴,结交IT行业有缘之人

项目回忆
12月24日平安夜的这DY上午出去做工程啦,配置的是ASA5520的防火墙,地点在某邮政公司,这次做工程只有两个人,
我当然还有还有老大。在还没去之前,就在准备cisco防火墙的资料,回顾了一下防火墙配置的内容,大概有了细致的了解,想着这回去应该可以很快的解决吧。

我们走着去工程现场的,那里我们这里不是很远,走路大概20分钟就到了吧。
还好天气还是很不错的,有太阳外面暖暖的,跟上回做工程的天气一样好,还好这次地方不是很难找,一会就到了。
到了工程现场之后,就等那边的工程师给我们一个具体的要求,不一会那边的工程师就到了。

因为是圣诞节啊,所以工程师还戴着圣诞帽,挺有过节的气氛的。
大概了解到客户的需求,我们就准备开始配置防火墙了,看着需求DY感觉是不难,挺简单的,想着应该一会就好了。
没想到当我们配完之后要验证的时候,出现了问题。那就是PAT转换不成功,就是把一个网段的地址,转换成一个IP地址。
然后立马去检查配置,看过配置以后没有发现问题,但就是没有现象出来。
没办法,只有试一下用图形化界面去配置,也就是用SDM登录到防火墙上进行配置。
防火墙有一个管理接口,是出厂之前配好的IP地址,是192.168.1.0网段的,只要手动配置电脑IP地址,就可以用SDM来配置防火墙了。
配完成之后,我们再次去验证PAT转换是否成功,但结果是没有,不知道哪里出了问题。试了很多办法,就是转换不成功,也看了很多的资料,认为配置没有问题,但效果都不明显。
配到人家下班了,问题还是没有找出来,那就只好等着明天再来检查问题了。这时有人来送一送礼物了,当然没有我们的份啦,因为我们不是人家的员工啊。
客户那边下班了,我们没有解决问题,就只有明天再来了,希望明天可以很快的把问题解决了。
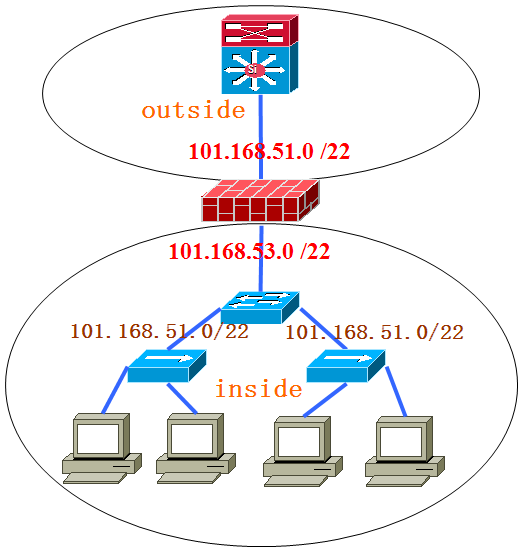
第二天找到了问题的所在,其实客户要求方面有点问题,如果按他们的方法把内网设置成outside而外网设置成intside,也就是说外网的安全级别比内网要高,可以实现效果就必须做静态NAT,做起来需要写很多个访空列表,配置起来比较繁琐。
如果改一下方向,配置起来就简单多了。final的实施的方案跟客户沟通之后就改了一下inside和outside的方向,NAT转换成功。
这次工程的印象实在是太深刻了,不仅在工程当中了解客户的需求之后,给出解决方案。
而且如果当客户给出的方案与实际中有差别的话,应立刻提出问题进行沟通并向客户进行说明,这样在做工程中就会事半功倍。
这次项目需求
1、内网访问外网作NAT转换成一个IP地址出去
2、交换机作为内网的网关
拓扑:
项目配置
ASA# sh running-config : Saved : ASA Version 7.2(3) ! hostname ASA domain-name default.domain.invalid enable password 8Ry2YjIyt7RRXU24 encrypted names dns-guard ! interface GigabitEthernet0/0 nameif inside security-level 100 ip address 101.168.53.160 255.255.255.192 ! interface GigabitEthernet0/1 nameif outside security-level 0 ip address X.X.X.254 255.255.255.192 ! interface GigabitEthernet0/2 shutdown no nameif no security-level no ip address ! interface GigabitEthernet0/3 shutdown no nameif no security-level no ip address ! interface Management0/0 nameif management security-level 100 ip address 192.168.1.1 255.255.255.0 management-only ! passwd 2KFQnbNIdI.2KYOU encrypted ftp mode passive dns server-group DefaultDNS domain-name default.domain.invalid access-list 2 extended permit icmp any any access-list 2 extended permit tcp X.X.X.0 255.255.255.192 host 101.21.129.197 eq 100 access-list 2 extended permit tcp X.X.X.0 255.255.255.192 host 101.21.129.197 eq 101 access-list 2 extended permit tcp X.X.X.0 255.255.255.192 host 101.21.129.197 eq 102 access-list 2 extended permit tcp X.X.X.0 255.255.255.192 host 101.21.129.197 eq 103 access-list 2 extended permit tcp X.X.X.0 255.255.255.192 host 101.21.129.197 eq 104 access-list 2 extended permit tcp X.X.X.0 255.255.255.192 host 101.21.129.197 eq 105 access-list 2 extended permit tcp X.X.X.0 255.255.255.192 host 101.21.129.196 eq 100 access-list 2 extended permit tcp X.X.X.0 255.255.255.192 host 101.21.129.196 eq 101 access-list 2 extended permit tcp X.X.X.0 255.255.255.192 host 101.21.129.196 eq 102 access-list 2 extended permit tcp X.X.X.0 255.255.255.192 host 101.21.129.196 eq 103 access-list 2 extended permit tcp X.X.X.0 255.255.255.192 host 101.21.129.196 eq 104 access-list 2 extended permit tcp X.X.X.0 255.255.255.192 host 101.21.129.196 eq 105 access-list 2 extended permit tcp X.X.X.0 255.255.255.192 host 101.21.130.200 eq www access-list 2 extended permit tcp X.X.X.0 255.255.255.192 host 101.21.130.201 eq www access-list 2 extended permit tcp X.X.X.0 255.255.255.192 host 101.21.130.202 eq www access-list 2 extended permit tcp X.X.X.0 255.255.255.192 host 101.12.130.203 eq www access-list 2 extended permit tcp X.X.X.0 255.255.255.192 host 101.21.130.204 eq www access-list 2 extended permit tcp X.X.X.0 255.255.255.192 host 101.21.130.205 eq www access-list 2 extended permit tcp X.X.X.0 255.255.255.192 host 101.21.130.206 eq www pager lines 24 logging asdm informational mtu inside 1500 mtu outside 1500 mtu management 1500 no failover icmp unreachable rate-limit 1 burst-size 1 asdm image disk0:/ASDM-523.BIN no asdm history enable arp timeout 14400 nat-control global (outside) 1 X.X.X.250 netmask 255.255.255.192 nat (inside) 1 X.X.X.0 255.255.255.192 access-group 2 in interface outside route outside 101.21.129.197 255.255.255.255 X.X.X.252 1 route outside 101.21.129.196 255.255.255.255 X.X.X.252 1 route outside 101.21.130.200 255.255.255.255 X.X.X.252 1 route outside 101.21.130.201 255.255.255.255 X.X.X.252 1 route outside 101.21.130.202 255.255.255.255 X.X.X.252 1 route outside 101.21.130.203 255.255.255.255 X.X.X.252 1 route outside 101.21.130.204 255.255.255.255 X.X.X.252 1 route outside 101.21.130.205 255.255.255.255 X.X.X.252 1 route outside 101.21.130.206 255.255.255.255 X.X.X.252 1 timeout xlate 3:00:00 timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02 timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00 timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00 timeout uauth 0:05:00 absolute http server enable http 192.168.1.0 255.255.255.0 management no snmp-server location no snmp-server contact snmp-server enable traps snmp authentication linkup linkdown coldstart telnet timeout 5 ssh timeout 5 console timeout 0 dhcpd address 192.168.1.2-192.168.1.254 management dhcpd enable management ! ! class-map inspection_default match default-inspection-traffic ! ! policy-map type inspect dns migrated_dns_map_1 parameters message-length maximum 512 policy-map global_policy class inspection_default inspect dns migrated_dns_map_1 inspect ftp inspect h323 h225 inspect h323 ras inspect rsh inspect rtsp inspect esmtp inspect sqlnet inspect skinny inspect sunrpc inspect xdmcp inspect sip inspect netbios inspect tftp ! service-policy global_policy global username cisco password 3USUcOPFUiMCO4Jk encrypted prompt hostname context Cryptochecksum:b3ff4228ee79bc0299b4a34ed40fb3b2 : end ASA# sh route Codes: C - connected, S - static, I - IGRP, R - RIP, M - mobile, B - BGP D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2 E1 - OSPF external type 1, E2 - OSPF external type 2, E - EGP i - IS-IS, L1 - IS-IS level-1, L2 - IS-IS level-2, ia - IS-IS inter area * - candidate default, U - per-user static route, o - ODR P - periodic downloaded static route Gateway of last resort is not set C 101.168.5.0 255.255.255.192 is directly connected, inside C 101.168.5.192 255.255.255.192 is directly connected, outside S 101.21.129.197 255.255.255.255 [1/0] via X.X.X.252, outside S 101.21.129.196 255.255.255.255 [1/0] via X.X.X.252, outside S 101.21.130.206 255.255.255.255 [1/0] via X.X.X.252, outside S 101.21.130.204 255.255.255.255 [1/0] via X.X.X.252, outside S 101.21.130.205 255.255.255.255 [1/0] via X.X.X.252, outside S 101.21.130.202 255.255.255.255 [1/0] via X.X.X.252, outside S 101.21.130.203 255.255.255.255 [1/0] via X.X.X.252, outside S 101.21.130.200 255.255.255.255 [1/0] via X.X.X.252, outside S 101.21.130.201 255.255.255.255 [1/0] via X.X.X.252, outside
本文出自 网络工程师培训、思科认证、华为认证培训-onelab网络实验室 ,原文链接:https://www.xacisco.net/4631 。如若转载请注明出处。